You’ve probably seen a movie based in medieval times where a king sends a letter across the land to someone important using a messenger.
Before he gives the letter to the messenger, he rolls it up, drips some hot wax on it, and seals it with his fancy gold ring, as you’d expect.
And it’s everyone’s expectation that only the recipient will break that seal, am I right? TRUST.
It’s exceptionally devious and cunning when the letter tells the recipient to kill the messenger, but that’s another story.
If that seal gets broken by someone else, deep down there’s at least a bit of outrage. Trust was broken. “That shouldn’t happen!” we say to ourselves.
Well, guess what? It happens ALL THE TIME today.
But the letter is a form. The message is the data, and that wax and seal, well that’s like form security.
Passing data with forms is so ubiquitous that it’s one of those things we take for granted—nearly every web app on the planet needs to collect data through forms at some point or another in the user’s experience.
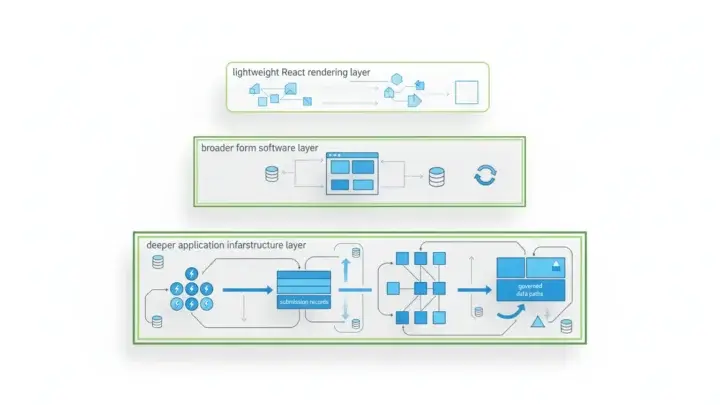
Because the concept of collecting data through a form is so simple, it often obscures the complex challenges with form security that lurk underneath.
And let’s face it, we need something more than a bit of hot wax and noble trust to keep that data secure.
The sanctity of the data exchanged must be upheld.
So what is actually lurking underneath in terms of Form.io’s form security?
Let me explain.
Encryption
Encryption is a way to scramble data to appear as a meaningless, hot mess of gobbly-gook characters. But there’s a pattern to that madness and if you have the key, you can descramble (decrypt) the data so it can return to its original, sensible form.
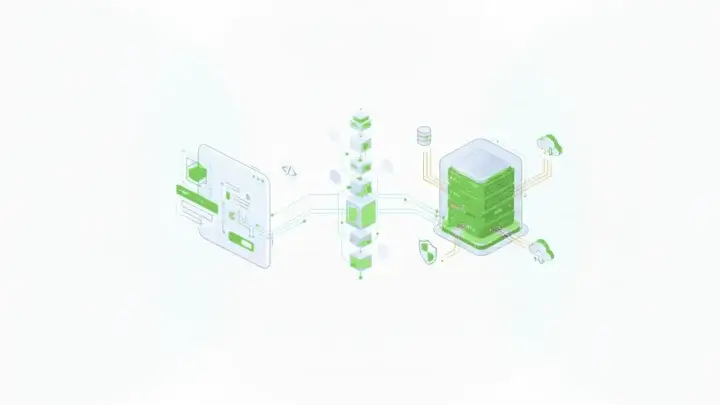
The process of encrypting and decrypting data happens behind the scenes automatically.
A lot of our customers are managing personally identifiable information (PII), and there are rules and regulations that govern that kind of data. In many scenarios, that data, such as emails, physical addresses, medical history, financial data, etc., needs to be encrypted.
Form.io supports both in-transit encryption and at-rest encryption. When data is being transferred, the data is encrypted, so even if it was snatched out of the lines of communication in transit, it’s not going to be readable.
Back in the day, people would discover passwords in a database just sitting there as plain text. It STILL happens today, but thankfully that’s a rare occurrence. Sensitive data that’s at rest should be encrypted while being stored, which Form.io lets you enable at the field level.
Authentication And Authorization
Some forms are open—no log in required, such as a survey. But for forms that are part of an application meant for only specific users, the application will need user registration and user login—which is done with a form of course.
That functionality is built-in to Form.io and can be done by connecting your existing authentication provider using SAML, OAuth, custom JWT Tokens, or something else.
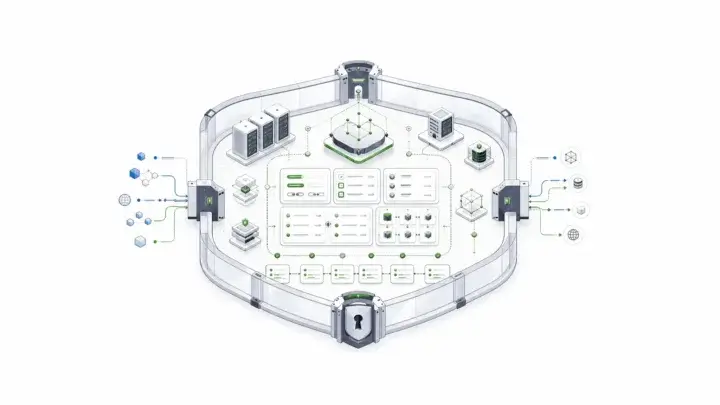
In addition, you can authorize certain users to only be able to access certain data and/or certain forms. This is also built-in.
When I say built-in, I mean that in a way where a non-developer can just modify some settings and you’re good to go—zero hassle.
And you can take it to the next level with Role-Based Access Control (RBAC).
Let’s say you have a database of users and those users have roles assigned to them (and again, this database doesn’t even need to be in Form.io), you can integrate that database with Form.io and then assign access to different forms and data based on their already-assigned roles.
This is especially helpful when you need to maintain an auditable record of accountability and it simply mitigates data from being mishandled. It’s like having guardrails for your users accessing data.
Form Security Industry Standards
Maybe you’ve heard of GDPR, HIPAA, or some other data and information privacy regulation. NGL, supporting these regulations can be a lot of work if you are building something from scratch, but there’s no need for that.
With Form.io’s Security and Compliance module, forms are compliant out of the box, again zero-hassle form security AND compliance.
Some Nice To Haves
These form security features are kind of like basic application rights. They’re not nice-to-haves, they’re mostly essential.
BUT…
Having them built for you is nice to have.
Being able to adjust security settings without having to write code is nice to have.
Enabling a non-developer configure security and access is nice to have.
Creating a new project that has the basic authentication pieces already built and configured is nice to have.
And all the other done-for-you things within Form.io is certainly nice to have.