If you’re building forms inside Claude Code, Cursor, Windsurf, or another agentic coding environment, the question is not whether to use MCP. It is which MCP server does the job you actually have.
That distinction matters because most “forms for AI” tools are solving different problems. Some manage a hosted form account. Some only read existing forms. Some route through middleware. Some help developers build. Others try to expose runtime workflows.
Those are not the same surface.
This guide ranks dev-time MCP servers for forms: the servers a developer points a coding agent at to generate, modify, validate, or inspect form infrastructure during application development. It also explains where runtime UAG fits, because production agents need a different governance layer after the form ships.
Two surfaces, not one
A form MCP can have two possible jobs.
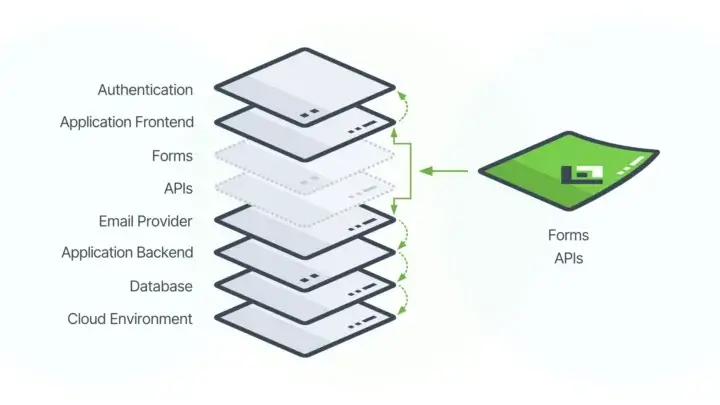
Dev-time MCP helps a developer build. A developer working in Claude Code, Cursor, Windsurf, or another coding environment asks an agent to generate or modify a form. The agent calls an MCP server, receives schema and tool context, and helps create or update assets the application owns. This is a build-time surface. It should be opinionated about schema, useful inside the IDE, compatible with source control, and safe enough not to damage existing production forms.
Runtime UAG helps an agent operate. A production agent executes a workflow that includes form logic: routing, validation, submission handling, data capture, approvals, or updates inside the application’s actual governance envelope. This is the runtime surface. It should inherit the auth, RBAC, validation, audit patterns, revision control, and deployment boundaries of the system around it.
A dev-time MCP that pretends to be a runtime governance layer is dangerous. A runtime gateway that pretends to be a developer tooling surface is awkward. They have different users, trust boundaries, and architectural requirements.
This is where the recent schema-driven application infrastructure argument matters. In regulated environments, the core problem is not just form creation speed. The problem is governance drift. AI-assisted developers can generate applications faster than governance teams can review them, and runtime agents can act inside workflows faster than auditors can sample them. The white paper’s answer is a governed, JSON-based schema as the source of truth for forms, APIs, validation, human interfaces, and agentic context.
That is why dev-time and runtime both matter. Build-time agents should create against the governed schema pattern. Runtime agents should operate through the governed schema surface. The easy path and the governed path need to be the same path.
Formio is the only entry in this forms ranking that currently has both surfaces as distinct products: a dev-time MCP server for developers building forms, and Universal Agent Gateway (UAG) for runtime agentic workflows. UAG does not belong inside the dev-time ranking as though it were the same product. Its existence is still important because it answers the question most form MCP comparisons avoid: what happens after the form ships?
The ranking

- Formio dev-time MCP server — vendor-maintained, open-source, self-hostable, full form CRUD, and paired with a separate runtime governance surface.
- Jotform MCP — hosted, OAuth-based, vendor-maintained, useful for managing forms inside a Jotform account.
- Tally MCP — hosted, OAuth/API-key based, beta, useful for lightweight form creation and submission access.
- Typeform MCP — vendor-maintained beta with limited form read access and contact write access.
- Retool MCP for the forms path — official but read-focused; useful for inspecting Retool orgs, not a forms-first schema layer.
- n8n MCP Server Trigger — flexible workflow exposure, self-hostable, but not form-native.
- Zapier MCP / Pipedream MCP gateways — broad middleware access to many app APIs, but not vendor-native form infrastructure.
The short version: if your team is building form-driven application infrastructure, Formio is the strongest fit. If your team is managing forms inside an existing SaaS form account, Jotform or Tally may be enough. If your team needs generic workflow automation, n8n, Zapier, or Pipedream can help, but they are not form-native MCP servers.
The criteria that matter
MCP is an open standard for connecting AI applications to external systems, tools, data sources, and workflows (Model Context Protocol docs). Anthropic introduced MCP as a way to replace fragmented one-off integrations with a standard method for connecting AI assistants to systems where data lives, including content repositories, business tools, and development environments (Anthropic).
That standard matters. But for forms, the standard connection layer is only the beginning. A dev-time form MCP has to answer six harder questions.
1. Can the AI generate and modify forms, or only read them?
Read-only MCP servers are useful for inspection. They are not enough for developers building applications.
A coding agent needs to create forms, update forms, inspect schema, validate components, and avoid destructive changes to existing assets. If a server can only list forms or fetch submissions, it may be a helpful assistant for account management, but it is not a serious dev-time form-building surface.
2. What schema is underneath?
For application infrastructure, schema portability matters.
A proprietary form JSON object may work well inside one hosted product. It becomes a constraint when the application needs to own its forms, APIs, submissions, validation rules, and workflow behavior over time.
Formio’s advantage is not merely that forms are represented as JSON. The stronger distinction is the atomic component model: one JSON object can carry structure, validation, conditional logic, calculated values, rendering intent, and labeling intent together. That keeps shape and behavior closer to the same contract, instead of forcing teams to rebuild behavior in separate code paths.
3. Can you self-host?
Hosted-only MCP servers route form definitions, submissions, and tool calls through vendor infrastructure. That may be fine for a lightweight marketing form. It can be a non-starter for healthcare, public sector, financial services, or air-gapped environments.
Teams already evaluating self-hosted Formio usually ask the right question: can this run inside the environment where the governed system already lives?
4. Is it vendor-maintained or community-built?
Community wrappers can be useful for experimentation. Production tooling needs a maintainer who understands the underlying product and its API changes.
For form workflows, this matters because a quiet schema change or permission change can break more than a demo. It can break the layer where structured data enters an application.
5. Does the vendor have a runtime answer?
A dev-time MCP helps create or modify forms. It does not automatically govern what production agents do after those forms are deployed.
That is why runtime matters as a separate criterion. If the vendor’s only answer is a build-time server, the burden of production agent governance shifts back to your application team. If the vendor has a distinct runtime surface, the architecture is at least acknowledging that production agents need different controls from coding agents.
6. Is it discoverable where developers search?
Developers find MCP servers in client registries, GitHub, Smithery, mcp.so, Glama, PulseMCP, vendor docs, and coding-tool setup guides. Distribution is not architecture, but it affects adoption.
A good server still needs to be easy for developers to find, install, configure, and verify.
1. Formio dev-time MCP server
What it is. Formio’s dev-time MCP server enables AI assistants to interact with Formio’s API to create, read, update, and manage forms using natural language. The public README lists tools for listing forms, retrieving form details, creating forms, updating forms, deleting forms, and building properly structured Formio components. It also includes safety guardrails so the MCP can modify only forms it created, protecting existing forms from accidental changes (Formio MCP GitHub).
The server supports stdio transport for Claude Desktop-style clients and HTTP transport for HTTP-capable clients or remote access. It uses Formio project credentials through an API key or JWT token.
Scorecard
| Criterion | Formio dev-time MCP |
| Read + write | Create, read, update, delete, and component-building tools |
| Schema | Formio JSON schema / schema-driven form infrastructure |
| Self-hosted | Yes, deployable by the customer |
| Vendor-maintained | Yes |
| Runtime answer | Yes — UAG, as a separate runtime product |
| Directory presence | GitHub now; broader directory distribution should be verified before publication |
Why it is #1
Formio wins this ranking because it treats forms as application infrastructure, not just hosted assets in an account.
At dev time, the MCP server gives coding agents structured access to the forms layer: list forms, inspect schemas, create forms, update MCP-created forms, delete MCP-created forms, and build components. That is the right shape for Claude Code, Cursor, or Windsurf because the developer is still building the application.
The safety guardrail is also important. The README states that Formio MCP prepends `[MCP]` to form titles and `mcp-` to form paths for created forms, then rejects update or delete attempts against non-MCP forms. That is exactly the kind of boring constraint AI coding tools need. It prevents the agent from treating a real project like a sandbox.
The larger reason Formio ranks first is the dev-time/runtime separation. Formio’s MCP server is for building. UAG is for runtime agentic workflow execution. A vendor that ships both surfaces is making a stronger architectural claim than a vendor that ships one MCP endpoint and hopes it covers everything.
Where it falls short
Distribution is the current weak spot. The server is available on GitHub and can be run with Formio project credentials, but directory presence should be checked before the final WordPress update. Developers searching inside specific MCP directories may not find it everywhere yet.
The article should also avoid pretending dev-time MCP automatically makes runtime workflows safe. It does not. Dev-time MCP helps build against the schema pattern. Runtime governance belongs to UAG and the surrounding Formio deployment, permissions, validation, and audit design.
Best for
Developers building forms inside Claude Code, Cursor, Windsurf, or similar tools when the form is part of the application, not just a hosted object in a third-party form account.
It is especially relevant for teams that care about embedded forms and APIs, self-hosted deployment, governed submissions, and long-term schema ownership.
2. Jotform MCP
What it is. Jotform’s official MCP server exposes Jotform forms and submissions through a hosted endpoint at `https://mcp.jotform.com`. Jotform documents five standard tools: `form_list`, `create_form`, `edit_form`, `create_submission`, and `get_submissions`. It uses OAuth and requires one-time approval for each user (Jotform MCP docs).
Jotform also documents an MCP App variant with interactive UI components for visual form building, previews, browsing forms, and working with submissions inside MCP-App-capable clients.
Scorecard
| Criterion | Jotform MCP |
| Read + write | Create/edit forms, create submissions, fetch submissions |
| Schema | Jotform form model |
| Self-hosted | No; local server capabilities are described as in development for enterprise |
| Vendor-maintained | Yes |
| Runtime answer | Jotform-hosted form runtime, not a separate runtime agent governance layer |
| Directory presence | Official docs and hosted endpoint |
Why it is #2
Jotform has one of the clearer vendor-maintained MCP stories in the category. OAuth is documented. The remote endpoint is simple. The five-tool surface covers the core account-management jobs most Jotform users will want from an AI assistant.
For teams already living inside Jotform, this is a reasonable on-ramp. The assistant can list forms, create a form, edit a form, create a submission, or fetch submissions without the team building a custom connector.
Where it falls short
It is still a Jotform account-management surface. The application does not own the form infrastructure in the same way it would with a self-hosted schema-driven platform. The MCP server helps operate inside Jotform; it does not turn Jotform into an application-owned schema layer.
Jotform’s enterprise section mentions SSO, access control, higher rate limits, custom branding, and dedicated support. It also says local server capabilities are actively being developed. That is useful, but it is not the same as a current self-hosted dev-time plus runtime governance architecture.
Best for
Teams already using Jotform who want AI-assisted form management and submission access. It is not the strongest foundation for form-driven applications that need to live inside the customer’s own infrastructure.
3. Tally MCP
What it is. Tally’s MCP server is a hosted beta server at `https://api.tally.so/mcp`. The docs say it can build Tally forms, retrieve forms, and fetch submissions using natural language through assistants like Claude. Tally supports OAuth and API-key authentication, with setup examples for Claude Desktop, Claude Code, and Cursor (Tally MCP docs).
Scorecard
| Criterion | Tally MCP |
| Read + write | Create and update forms, list forms, fetch submissions |
| Schema | Tally form model |
| Self-hosted | No |
| Vendor-maintained | Yes, beta |
| Runtime answer | None beyond the Tally hosted product |
| Directory presence | Official docs and Claude/Cursor setup examples |
Why it is #3
Tally is credible for lightweight form building because the MCP server can create and update forms directly, not only read them. The setup story is practical, especially for Claude Code and Cursor users.
For small teams, prototypes, internal surveys, and low-governance forms, that may be enough.
Where it falls short
The docs explicitly mark the MCP server as beta. Tally is also hosted-only, which limits its fit for enterprise infrastructure requirements. There is no separate runtime governance answer for production agents operating against form workflows.
That is not a criticism of Tally’s core product. It is a fit distinction. Tally can be a good lightweight form tool and still be the wrong infrastructure choice for governed enterprise workflows.
Best for
Solo developers and small teams that want AI-assisted Tally form creation without self-hosting or regulated-workflow requirements.
4. Typeform MCP
What it is. Typeform’s MCP server is an early-access beta connector for interacting with a Typeform account from an LLM client. Typeform says it currently supports basic read-only access to forms and basic read-write access to contacts. Authentication currently uses a personal access token; OAuth support is on the roadmap (Typeform MCP docs).
Scorecard
| Criterion | Typeform MCP |
| Read + write | Basic read-only forms; basic read-write contacts |
| Schema | Typeform form model |
| Self-hosted | No |
| Vendor-maintained | Yes, beta |
| Runtime answer | None |
| Directory presence | Emerging |
Why it is #4
Typeform has brand recognition and a real vendor-maintained MCP beta. That matters. It means the MCP story is not only a third-party wrapper.
Where it falls short
For form-building with AI, the current tool surface is too limited. Read-only form access does not satisfy the dev-time form generation use case. Personal access token authentication is also a current-state limitation compared with OAuth-based flows.
Until the tool surface expands, Typeform MCP is better understood as an early connector than a production-ready form-building MCP.
Best for
Typeform users who want to experiment with an official beta and can tolerate limited capabilities.
5. Retool MCP for the forms path
What it is. Retool’s official MCP server is an admin-oriented beta that lets AI agents inspect and query a Retool organization, including apps, automations, resources, users, and related assets. Retool described the initial release as read-focused for admins, with expanded capabilities planned based on beta feedback (Retool community announcement).
Scorecard
| Criterion | Retool MCP |
| Read + write | Read-focused beta |
| Schema | Retool app/resource model |
| Self-hosted | Retool deployment model varies; MCP specifics should be verified per deployment |
| Vendor-maintained | Yes |
| Runtime answer | Retool agents / broader Retool platform story, not forms-first UAG |
| Directory presence | Retool ecosystem |
Why it is #5
Retool is a credible platform for internal-tool teams. If your forms exist as part of Retool apps, an MCP server that can inspect the Retool organization may be useful.
Where it falls short
This is not a forms-first MCP server. Retool is a general internal-app platform, and the MCP server reflects that. It helps inspect a Retool environment; it does not primarily generate application-owned forms against a portable form schema.
Best for
Retool-centric teams that want AI visibility into their internal-tool footprint. Not teams looking for a form infrastructure layer.
6. n8n MCP Server Trigger
What it is. n8n’s MCP Server Trigger node lets n8n act as an MCP server, making n8n tools and workflows available to MCP clients. The node exposes a URL clients can call, supports test and production URLs, and can require bearer or header authentication. n8n also notes deployment caveats around SSE or streamable HTTP when running with multiple webhook replicas (n8n MCP Server Trigger docs).
Scorecard
| Criterion | n8n MCP Server Trigger |
| Read + write | Whatever the exposed workflow allows |
| Schema | Workflow-defined |
| Self-hosted | Yes, if n8n is self-hosted |
| Vendor-maintained | Yes |
| Runtime answer | n8n workflows, same general surface |
| Directory presence | n8n ecosystem |
Why it is #6
n8n is flexible. If your team already runs n8n, exposing a workflow as an MCP server is a natural extension. It can be a useful bridge between agents and existing automations.
Where it falls short
It is not a form MCP. It is a way to expose workflows through MCP. Developers can build something form-shaped with it, but the schema, validation, submission model, and governance pattern are whatever the team designs.
That is useful flexibility for automation teams. It is not a shortcut to schema-driven form infrastructure.
Best for
n8n shops exposing existing workflows to agents. Not teams that need a forms-first dev-time MCP.
7. Zapier MCP / Pipedream MCP gateways
What they are. Zapier MCP connects AI tools to thousands of apps through Zapier’s existing app ecosystem. Zapier positions it as one governed connection for AI agents such as Claude, ChatGPT, and Cursor, with account-level restrictions, managed connections, and workspace controls (Zapier MCP). Pipedream offers a similar broad integration posture across app APIs, though public fetch access to the MCP page is less readable from this environment.
Scorecard
| Criterion | Zapier / Pipedream MCP gateways |
| Read + write | Whatever the underlying app/API allows |
| Schema | Inherits from the wrapped vendor |
| Self-hosted | No |
| Vendor-maintained | Gateway-maintained, not form-vendor-native |
| Runtime answer | Gateway workflow controls, not form-native runtime governance |
| Directory presence | Strong |
Why they are #7
They exist, they are broad, and they can be practical when the form tool you use does not have its own MCP server. For teams already standardizing on Zapier or Pipedream, the gateway path can be faster than waiting for every vendor to ship a first-party MCP.
Where they fall short
A gateway is still a gateway. It does not know forms as a primitive unless the underlying app API exposes that structure clearly. It inherits the wrapped vendor’s schema, auth model, rate limits, task costs, and workflow constraints.
For production form infrastructure, this adds another layer rather than clarifying the contract.
Best for
Teams that need AI access to many SaaS apps and can accept gateway latency, task cost, and inherited vendor constraints.
Honorable mentions that are not really in the category
Google Forms, Microsoft Forms, and SurveyMonkey. No first-party forms MCP story strong enough to treat them as category leaders here. Gateway wrappers or community connectors may exist, but they are not the same as vendor-maintained form infrastructure.
Community Jotform, Paperform, Gravity Forms, and similar wrappers. Useful for experimentation. Riskier for production because maintenance, auth behavior, and schema changes can drift quietly.
Onform and new MCP-native form tools. Worth watching, but too early to evaluate for regulated-enterprise use without a longer product and deployment record.
Why runtime UAG is a separate evaluation

UAG should not be ranked as though it were the same thing as a dev-time MCP server. It has a different job.
Formio’s UAG documentation says Universal Agent Gateway uses MCP to enable Formio functionality through an AI agent workflow and provides agents with dynamic context for using Formio JSON forms. It describes UAG as the package sitting between the Formio Platform and the AI agent, including the stock MCP server, authorization infrastructure, and custom tools or modules (Formio UAG docs).
That is runtime language. UAG is about agents operating against forms, fields, and submissions in a project. The standard tool set includes:
- `get_forms`, which returns forms tagged for UAG use
- `get_form_fields`, which gives the agent a high-level overview of the fields needed to submit a form
- `get_field_info`, which provides validation, conditionals, input formats, and field structure
- `collect_field_data`, which helps gather required information from the user
- `confirm_form_submission`, which confirms collected information before submission
- `submit_completed_form`, which creates the form submission
- `find_submissions`, which queries submissions from natural language intent
- `submission_update`, which updates existing submissions when allowed
The UAG landing page frames this as JSON schemas becoming agent context: form definitions, validation rules, conditional logic, data models, RBAC policies, auth integration, form settings, and data routing become the binding set of rules for agents (Formio UAG).
That is the runtime distinction. A coding agent creating a form needs a dev-time MCP. A production agent collecting intake data, finding submissions, or updating records needs a runtime gateway that works through the form and submission layer rather than around it.
What schema-driven infrastructure changes
The white paper’s most useful contribution is the distinction between a document validation schema and an application infrastructure schema.
A document validation schema defines shape. An application infrastructure schema must define shape, behavior, cross-runtime rendering, and network-transportable meaning. It needs to survive the trip from builder to renderer to API to runtime agent without losing the rules that make the workflow governed.
This matters for MCP because agents do not need more generic text. They need structured context they can act on safely.
In Formio, the atomic component is the key architectural unit. A field can carry type, structure, validation, conditional logic, calculated values, rendering intent, and labeling intent together. A repeating container such as an Edit Grid or Data Grid can carry nested child components with their behavior inline. Reused components carry behavior and governance with them.
For dev-time MCP, that means the coding agent is not merely generating a visual form. It is generating against the same schema pattern that defines API behavior and submission handling. For runtime UAG, it means the production agent can ask what fields exist, what validation applies, what input is missing, and what submission shape is required.
The same contract matters at both surfaces.
MCP safety: practical rules before agents touch real systems

The difference between dev-time MCP and runtime UAG does not remove the need for safety. It clarifies where safety belongs.
OWASP’s LLM Top 10 warns that prompt injection can lead to unauthorized access, tool misuse, data disclosure, execution of arbitrary commands in connected systems, and manipulation of critical decisions. It also calls out indirect prompt injection from external sources such as websites or files (OWASP LLM01:2025).
IBM’s 2025 Cost of a Data Breach report shows why this is not theoretical governance theater: 63% of organizations lacked AI governance policies to manage AI or prevent shadow AI, and 97% of organizations that reported an AI-related security incident lacked proper AI access controls (IBM).
Use these rules before connecting MCP servers to real systems.
Start read-only when possible
Read-only access is not harmless, but it is a safer starting point. Let agents inspect schemas, docs, forms, or submissions before granting write capabilities.
For dev-time form generation, write access may be necessary. That is why Formio MCP’s guardrail around MCP-created forms matters: the agent can create and modify its own generated forms without receiving blanket authority over every form in the project.
Scope credentials tightly
Do not hand an MCP server a broad production token unless the workflow truly requires it.
Use project-level credentials, narrow scopes, user-specific OAuth grants, or environment-specific API keys wherever possible. Separate dev, staging, and production access.
Require human approval for high-risk actions
Creating a draft form in a dev project is not the same as updating a production intake workflow.
Require human confirmation before destructive actions, submission updates, workflow changes, external sends, or production writes. Formio UAG’s `confirm_form_submission` tool is an example of a runtime confirmation step inside the form workflow itself.
Separate trusted and untrusted context
Agents that read web pages, tickets, uploaded files, or submission text are reading untrusted content. Do not let that content silently steer tool use.
This matters when form workflows include uploaded documents, open text fields, or public intake channels. Treat user-provided content as data, not instructions.
Log the tool calls
If an agent can touch production data, the organization needs to know what happened.
Who initiated the action? Which tool was called? What data was retrieved? What submission was created or updated? Was confirmation required? Which identity or role allowed it?
Without those answers, MCP becomes another shadow integration layer.
Use existing governance artifacts where possible
The right answer is not to recreate governance in prompts.
Use the artifacts the application already trusts: schema, validation rules, roles, permissions, form revisions, submission records, staged promotion, and audit patterns. That is the schema-driven infrastructure argument in practical form.
Comparison table
| Server / category | Primary job | Best fit | Governance strength | Write-risk level |
| Formio dev-time MCP | Generate and manage Formio forms during development | Developers building application-owned forms | Strongest dev-time fit; separate UAG runtime answer | Medium; constrained by MCP-created-form guardrails |
| Jotform MCP | Manage forms and submissions in Jotform | Existing Jotform teams | Good account-level OAuth story | Medium; hosted account writes |
| Tally MCP | Create/update lightweight Tally forms | Solo developers and small teams | Basic hosted-account governance | Medium; beta hosted writes |
| Typeform MCP | Read forms and manage contacts | Typeform beta experimenters | Limited current surface | Low-to-medium; limited form writes currently |
| Retool MCP | Inspect Retool org assets | Retool admins and internal-tool teams | Admin visibility, not forms-first governance | Low currently because read-focused |
| n8n MCP Server Trigger | Expose workflows as MCP tools | n8n automation teams | Depends on workflow design | Variable; whatever the workflow allows |
| Zapier / Pipedream MCP | Gateway access to many SaaS APIs | Teams needing broad app connectivity | Gateway/workspace controls, not form-native | Variable; inherited from each app |
When Formio should be on your shortlist

Formio should be on your shortlist when forms are part of the application contract.
That includes:
- regulated intake workflows
- healthcare referrals and patient onboarding
- government benefit applications or service requests
- customer onboarding and KYC
- insurance claims and policy intake
- internal service requests that trigger downstream workflows
- multi-tenant applications where customers need embedded or white-labeled form creation
- any workflow where submissions, validation, roles, and revisions need to remain governed over time
The difference is ownership. If your team just needs to create a survey in a hosted account, Formio is probably more infrastructure than you need. If your forms define data models, APIs, validation rules, user-facing interfaces, and agentic context, then the form layer is no longer a convenience tool. It is part of the application stack.
That is where Formio’s form builder and APIs, form validation and conditional logic, teams and permissions, and self-hosted deployment become relevant to the MCP decision.
The G2 review line used in the earlier draft still captures the fit well: “The form.io design is intuitive and easy to use but also has the advanced capabilities needed for our more complex client requirements.” That is the point. The right buyer is not looking for the simplest possible form tool. They are looking for a form layer that will not collapse when real application requirements arrive.
Key takeaways
- Dev-time MCP and runtime UAG are different surfaces. Do not evaluate them as one product.
- Dev-time MCP helps coding agents generate, inspect, and modify forms during application development.
- Runtime UAG helps production agents operate through governed form, field, submission, and workflow context.
- Formio ranks first because it treats both surfaces as real architectural problems.
- Hosted form MCPs can be useful, but they usually keep forms inside the vendor’s account model.
- For regulated or self-hosted workloads, schema ownership, permissions, validation, and auditability matter more than quick setup.
- The strongest architecture makes the easy path and the governed path the same path.
FAQ
What is an MCP server?
An MCP server exposes tools, data, or workflows to an AI application through the Model Context Protocol. Instead of building a custom connector for every AI assistant and every system, teams can expose capabilities through a standard protocol that MCP-capable clients can call.
For forms, an MCP server might list forms, create forms, update form schemas, fetch submissions, or expose form-related workflow actions.
What is the best MCP server for forms?
For application-owned forms, Formio’s dev-time MCP server is the strongest fit because it is vendor-maintained, open-source, self-hostable, and built around Formio’s schema-driven form infrastructure.
For teams already using a hosted form account, Jotform or Tally may be a better lightweight fit. The best choice depends on whether the form belongs to your application or to a third-party form account.
What is the difference between dev-time MCP and runtime UAG?
Dev-time MCP helps developers build. It belongs in tools like Claude Code, Cursor, or Windsurf and helps generate, inspect, or modify forms while the application is being developed.
Runtime UAG helps production agents operate. It belongs inside the application workflow and gives agents governed access to forms, fields, submissions, validation, and confirmation steps. Dev-time MCP is for building the form. Runtime UAG is for operating through the form after it ships.
Does UAG replace Formio’s dev-time MCP server?
No. UAG and the dev-time MCP server solve different problems.
The dev-time MCP server helps coding agents create and manage Formio forms during development. UAG provides runtime agent context and tools for production workflows. Treating them as interchangeable creates the exact confusion this category needs to avoid.
Are MCP servers safe for enterprise systems?
They can be, but safety depends on configuration, credential scope, deployment model, tool design, logging, and human approval for risky actions.
A server that is safe for reading documentation may not be safe for updating production submissions. Start with least privilege, separate development from production, and do not give agents broad write access without a clear approval and audit model.
Do MCP servers replace APIs?
No. MCP servers usually sit on top of APIs or application services. They give agents a structured way to discover and call capabilities, but the underlying system still needs stable APIs, authentication, authorization, validation, and logging.
In Formio’s case, MCP and UAG are valuable because they connect agents to the form and submission infrastructure rather than bypassing it.
Why does JSON schema matter for form MCP servers?
A coding agent needs structured context. JSON-based schemas can describe fields, validation, nesting, required values, and submission shape in a machine-readable format.
The stronger Formio argument goes beyond generic JSON Schema. Formio’s component model keeps field structure, validation, conditional logic, calculated values, rendering intent, and labeling intent together, which makes the schema more useful as application infrastructure.
Should agents have write access to forms?
Only when the workflow requires it and the boundary is clear.
For development, write access can be useful if the agent is creating or modifying sandboxed or MCP-created forms. For production, write access should require scoped credentials, runtime permissions, logging, and often human confirmation. A blanket production write token is not a governance strategy.
When should a team use Jotform or Tally instead?
Use Jotform or Tally when the form is meant to live inside that hosted form product and the team values fast setup over application-owned infrastructure.
Use Formio when the form is part of the application’s schema, API, submission, permission, or workflow layer, especially when self-hosting, embedded deployment, or regulated governance matters.
What should developers check before adopting a form MCP server?
Check whether the server can create and modify forms, what schema it uses, whether it can be self-hosted, who maintains it, what credentials it needs, whether it protects existing forms from accidental changes, and whether the vendor has a runtime answer for production agents.
The final question matters most: what happens after the form ships?
The actual decision
Three questions answer this for most teams.
Are you building forms inside an existing SaaS account or inside your own application? If the form belongs inside a hosted account, Jotform or Tally may be enough. If the form belongs to your application, Formio is the stronger architectural fit.
Does your data need to stay inside your infrastructure? If yes, start with Formio or a self-hosted workflow tool such as n8n. Hosted-only form MCPs will usually fail the deployment requirement before the feature comparison begins.
What happens after the form ships? This is the question most MCP-for-forms comparisons avoid. Dev-time generation is only half the story. Production agents need a runtime governance surface. If the answer needs to be “agents operate inside our application’s governance envelope, with schema, validation, permissions, submissions, and audit patterns aligned,” then Formio is the vendor in this category that has treated both halves of the problem seriously.
If your forms are already application infrastructure, your agent layer should respect that infrastructure too. Start with the Formio Universal Agent Gateway when production agents need governed access to real form workflows, or explore self-hosted Formio when the form layer needs to run inside your environment.
Try Formio for free